If you are looking to set up a Security Operations Center (SOC) function within your organization, it is wise to follow the NCSC factsheet: SOC inrichten: begin klein (Setting up a SOC: start small). It is a solid factsheet and I wholeheartedly agree with it, but I have two additions for organizations that use Microsoft 365. And there are quite a few of those.
My two additions to the NCSC factsheet are about focusing on the jackpot and working with the tools you already have.
Why not start BIG?
First, let me address this. The SOC function is something new for the organization. It is complicated and you need people who are already busy and have little to no experience with it. The SOC works with alerts that need to be investigated. An alert may indicate an incident, but it could also be a duplicate. Or a false positive. Or legitimate but not important. So you first need to figure out whether you even need to act on an alert, and only after that does the actual investigation begin. And after that comes the process of handling it with the relevant parts of the organization. How often can you realistically take that on in a day? Once? Or is even that too much?
In short, overloading the team with alerts will backfire. Within a foreseeable timeframe, the value of an alert will be reduced to something you can ignore. Exactly what you do not want.
So: start small. As Desmond Tutu, Dr. Leo Marvin, and Bob Wiley taught us.
Focus on the jackpot
First, the NCSC suggests monitoring "infrastructure or middleware components, such as the firewall, a web server, or the antivirus solution" as a starting point. I understand where this comes from and there is nothing inherently wrong with it as a starting point. But I personally think it makes more sense to start with whatever has the highest probability of abuse. For years, those were the logical components. But with the rise of cloud and SaaS, the majority of cyberattacks will not pass through a firewall or antivirus solution at all. After all: when an employee's user account falls into the wrong hands, an attacker can most likely log in from anywhere in the world to office.com or gmail.com and gain access to email.
And it just so happens that most cybercrime starts with email and often stays there. CEO fraud or BEC — the attacker only needs the mailbox, nothing else. Many ransomware incidents also start with leaked credentials, after which attackers move through the infrastructure without malware, acting as a colleague, and are barely distinguishable from a legitimate employee.
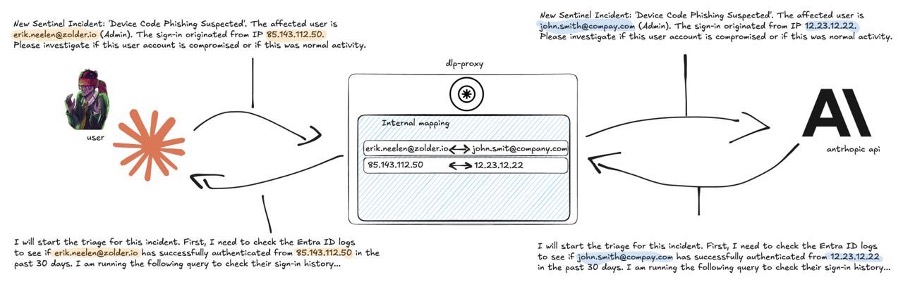
So my first step would be to make sure that authentication and usage of Office 365 / Microsoft 365 is monitored for abuse. That is where your organization's jackpot sits. Start there.
And if you do want to monitor the network — which is technically quite complex and will also generate a lot of false alerts — consider deploying a few Thinkst Canaries as tripwires in the network. We are happy to help.
Work with the tools you already have
The second point I want to make about the factsheet concerns the selection of a SIEM tool on page 6. I understand that an NCSC cannot easily recommend a specific tool, and that would not fit in a factsheet either. But let's be honest: you already have a SIEM tool. Your Microsoft 365 subscription automatically includes Microsoft Sentinel. It is not enabled by default, but it can be. Depending on how you use it, it may incur additional costs in your Microsoft subscription, but up to a significant level you can use the tool at no extra cost.
And if you feel some reluctance about jumping into vendor lock-in too quickly, consider this:
1. Microsoft Sentinel is seen by market analysts as a leader among SIEM providers.
2. The Microsoft Sentinel user community is by far the most active of any SIEM provider, which means a lot of knowledge is available from partners or even free online.
Attic Sentinel add-on
By now you will have gathered that Attic helps you set up a SOC function along exactly this line of thinking. Our alert focus is on abuse within the Microsoft 365 environment. Alert follow-up works the way you are used to with Attic, so your organization does not need to build up knowledge about operating Sentinel. And from this starting point, we can work with you to add more data sources to the monitoring. Check out our SOC-as-a-Service solution.